Force Chromecast and Google Home to use Pi-hole on pfSense
What we'll do:
- Forward all DNS requests to Pi-Hole
- Also known as DNS Hijacking
Why?
Even when setting your DNS servers within DHCP, Google IoT devices such as the Chromecast will use 8.8.8.8 anyway.
Lets get this under control and forward them to your Pi-hole instead!
Setup
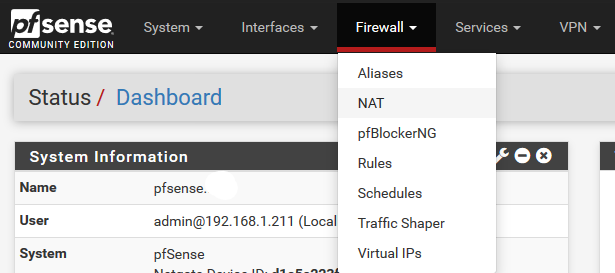
- Head to Firewall -> NAT -> Port Forward -> Add
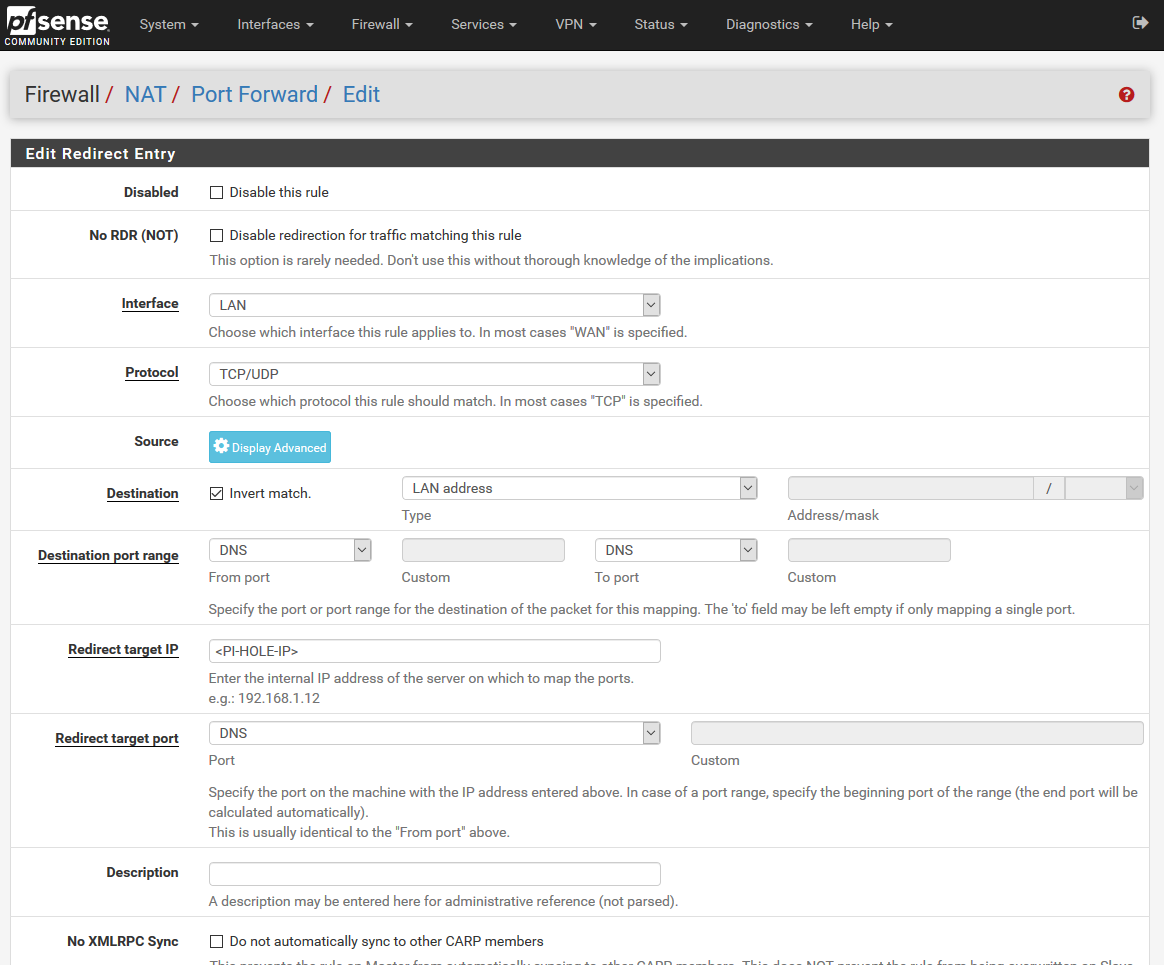
- Select the Interface LAN
- Protocol TCP/UDP
- Invert Match
- Select LAN Address
- Destination Port Range - DNS(53)
- Redirect target IP - PI Hole IP (Probably 192.168.x.x)
- Redirect target port - DNS(53)
- Now run:
Linuxdig example.com @8.8.8.8
Windowsnslookup example.com 8.8.8.8
You should now see example.com logged in your Pi-hole!
Cover Image Credit: https://unsplash.com/@farreal